Common Cyberattacks to Look For in The Age of AI

Artificial intelligence is changing financial services in many good ways. But it is also changing how cyberattacks are created.
For financial firms, cybersecurity is not only about protection. It is also about compliance, client trust, and business continuity. Regulations from the SEC and FINRA require firms to understand risks and document how they manage them.
Below, we explain what is changing and, more importantly, what you can do about it.
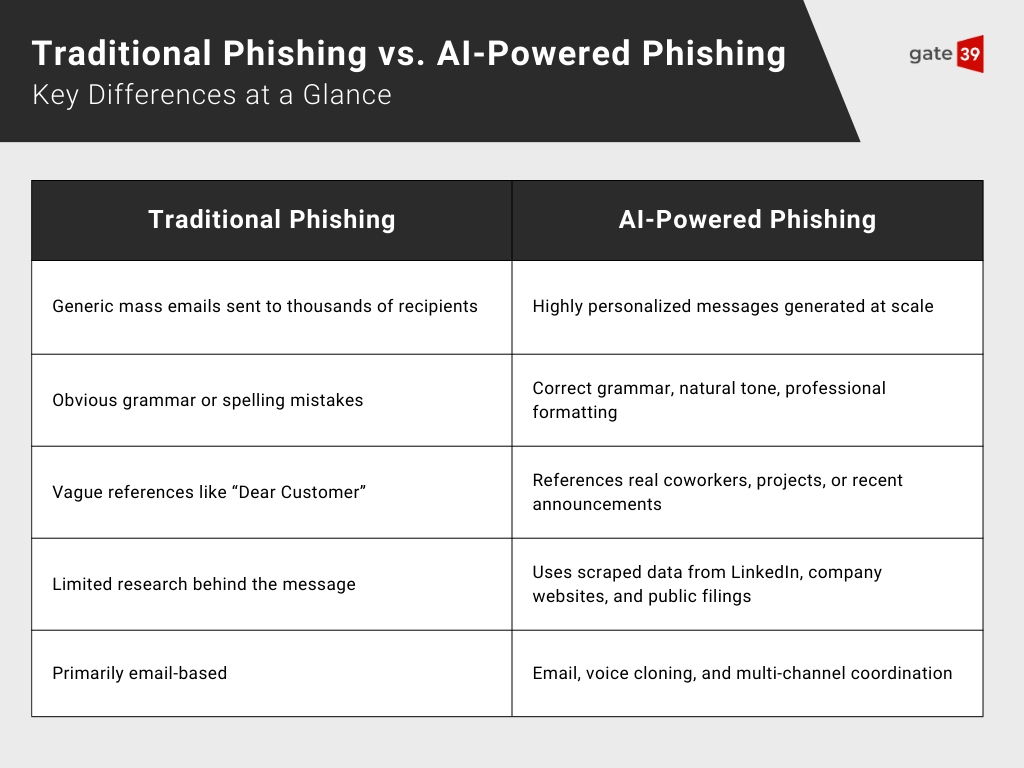
AI-Powered Phishing: The Evolution of Social Engineering
Phishing itself is not new, but what is new is how convincingly real it appears.
AI tools can now generate emails that match writing style, formatting, and tone. Attackers can scrape LinkedIn profiles, company websites, or press releases to reference real coworkers, projects, or recent announcements. This allows them to perform spear phishing at scale. Messages may reference real business relationships or recent events, and some attacks even combine email with AI-generated voice calls.
For a financial firm, one compromised credential can expose client portals, trading systems, or reporting tools.
The most effective strategy is to assume phishing will occur and design controls to contain its impact. The goal is simple: reduce exposure even if someone clicks.
Action steps you can take:
-
Enforce multi-factor authentication across all critical systems
-
Limit access by role so one login does not unlock everything
-
Email security should include behavior-based detection, not just keyword filtering
Deepfake Technology and Identity Verification Threats
Deepfake technology has also improved quickly. Video and audio can now be generated in ways that look convincing, especially over standard video calls.
In some cases, attackers have used AI-generated voice to impersonate executives and create urgency, such as demanding an immediate wire transfer or sensitive document. Social engineering works best when there is pressure, and AI makes that pressure easier to manufacture.
For firms that rely on remote onboarding, transaction approvals, or executive communications, identity verification needs to go beyond “face on screen.”
The answer is not to stop using video, but instead, look at implementing layered verification. Keep in mind that while security must support compliance, it also must support client experience. The balance matters.
Action steps you can take:
-
Require secondary confirmation for high-value transactions
-
Include liveness detection in biometric tools
-
Sensitive approvals should move through structured workflows instead of informal messages
Automated Vulnerability Exploitation and Zero-Day Attacks
AI-powered scanning tools can now analyze systems and identify weaknesses much faster than traditional methods. This reduces the time between a vulnerability becoming public and attackers attempting to exploit it.
Quarterly scans and slow patch cycles are often not enough anymore. A stronger approach includes continuous monitoring, risk-based patch prioritization, and clear system inventory.
Network segmentation also plays an important role. If one system is exposed, it should not automatically expose everything else.
Our managed hosting environments are structured with hardened configurations, ongoing monitoring, and defined patch workflows. Cybersecurity operates alongside performance and uptime, not separately from it.
Get started with our Cloud Services today >>
AI-Enhanced Ransomware and Data Exfiltration Techniques
Ransomware attacks are now more structured and selective. AI helps attackers map networks, identify sensitive files, and sometimes extract data before encryption. This creates both operational disruption and regulatory exposure.
Action steps you can take:
-
Isolate backups from production systems.
-
Regularly test recovery procedures instead of assuming they work
-
Monitor unusual data access patterns continuously
A Practical Path Forward for Financial Firms
As AI continues to evolve, so will cyber threats. The right response is preparation, discipline, and infrastructure designed with security in mind.
A strong cybersecurity program should include:
-
Clear visibility into systems and data
-
Strong identity controls
-
Continuous monitoring
-
Documented processes for compliance
-
Regular testing and improvement
But, you do not need a large in-house security team when security is built in by default at the infrastructure level.
At Gate 39, cybersecurity is an intrinsic part of our managed services. We design and manage environments specifically for regulated financial and agricultural firms. That means structured access control, hardened systems, monitored backups, and compliance-aware documentation.
If you want to evaluate how your hosting environment supports security and compliance, contact us to start a conversation.
You might also be interested in:
Editor’s Picks
Artificial intelligence is changing financial services in many good ways. But it is also changing how cyberattacks are created. For financial firms,...
Connect with us to discover how we can help your business grow.
.jpg)